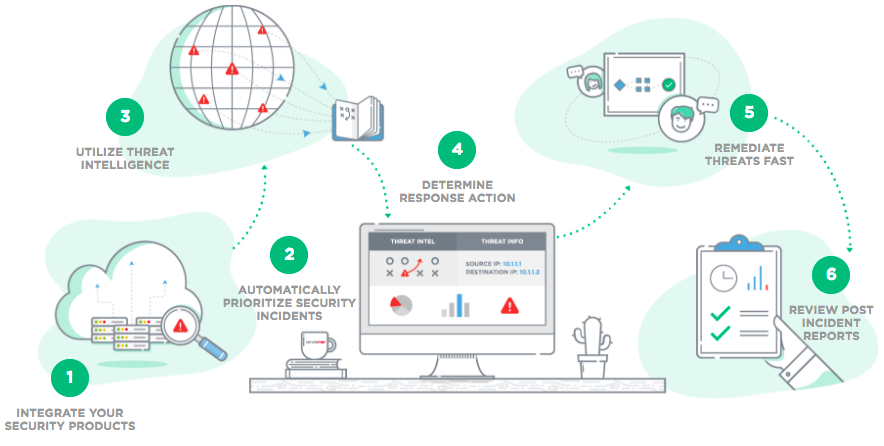
Threat Detection & Monitoring, Security Incident Response, Vulnerability Management, Compliance Support (PCI DSS)
- Detect fraudulent activity like unauthorized account access or money laundering attempts.
- Respond quickly to data breaches to minimize financial losses and reputational damage.
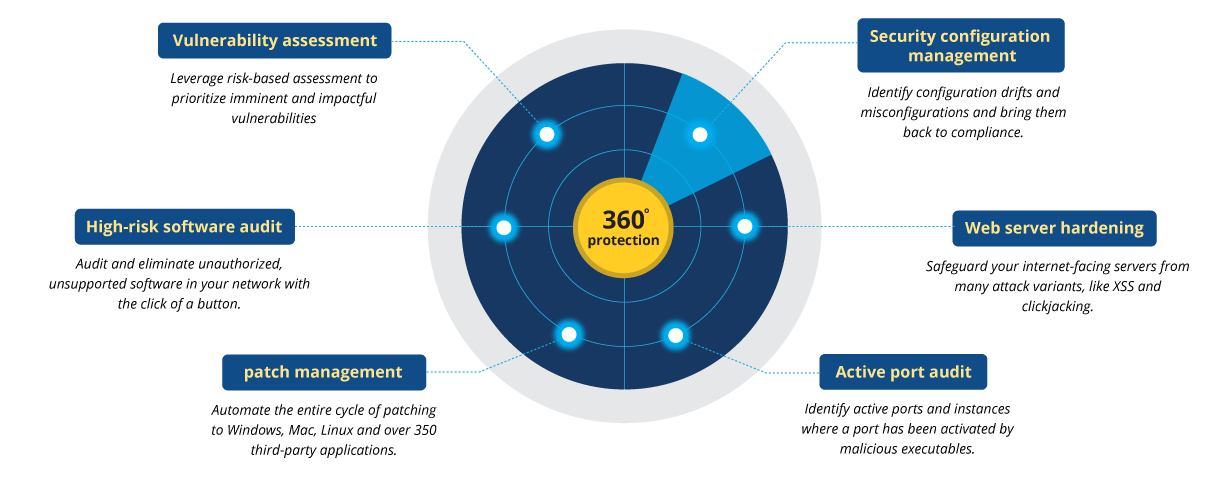
- Identify and patch vulnerabilities in online banking systems to prevent cyberattacks.
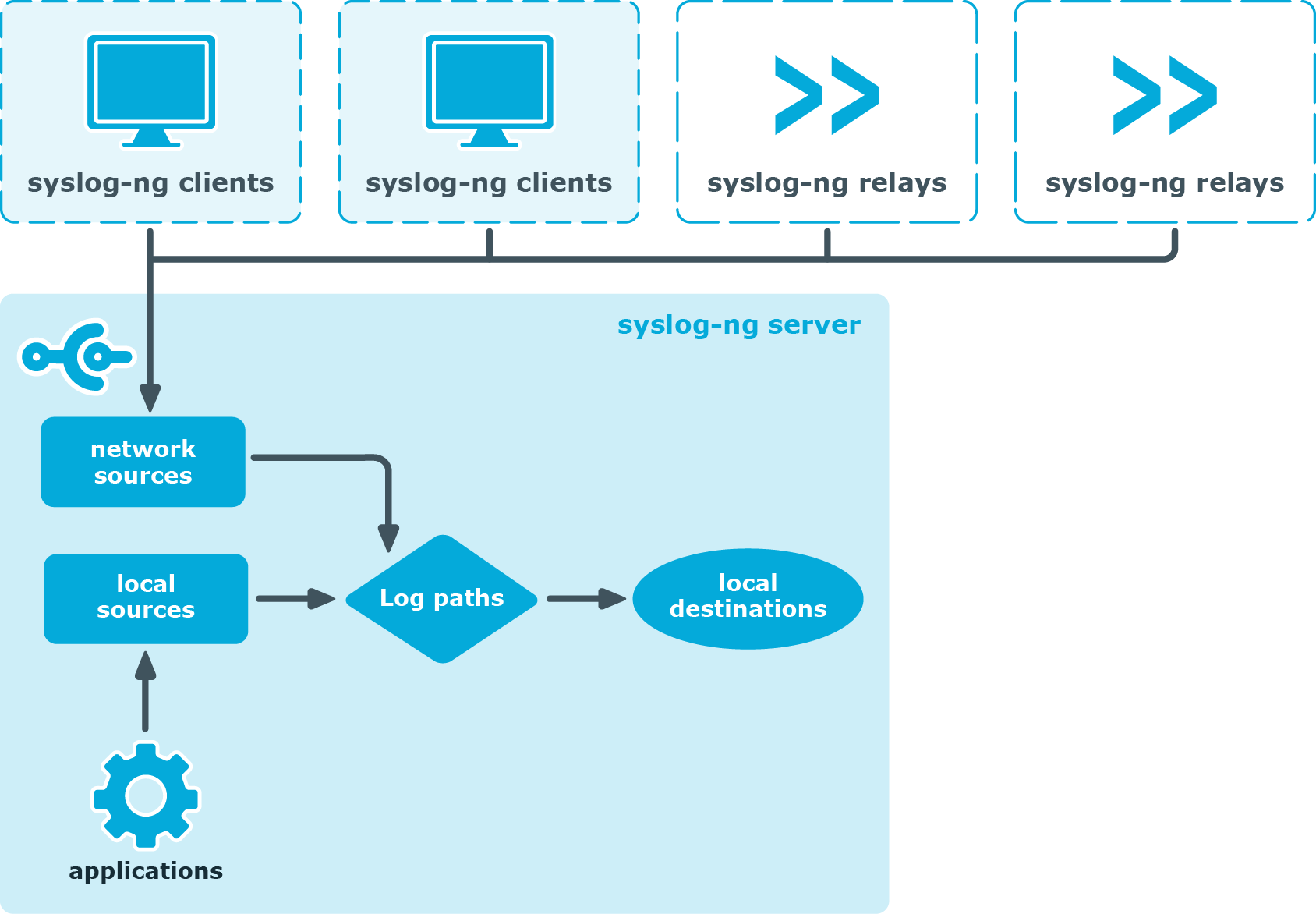
- Help achieve and maintain compliance with Payment Card Industry Data Security Standard (PCI DSS) through security control implementation and audit log management.